In March 2025, I was going through Shodan to investigate one of my clients’ security posture. During the investigation, I stumbled across a publicly accessible CCTV feed from a Finnish gas station. The feed did not require any authentication, allowing access to both live footage and recorded content. Notably, the cameras were positioned to capture not only the front door and the small grocery area but also the cashier area. Due to the sensitive nature of the feed, I decided to investigate further and determine the exact location of the gas station.
The location of the gas station couldn’t easily be determined by looking at the footage alone. With a bit of OSINT and overengineering, I was able to find the location of the gas station. This post describes the process and the tools used to find the location. For privacy reasons, all sensitive information has been redacted, and no screenshots of the actual footage are included in this post.
Table of contents
Open Table of contents
Looking for clues
Shodan didn’t provide too much useful information about the camera. In Finland IP geolocation’s are really inaccurate and it can show the location to the other side of the country. Although no logos or clear signs were visible in the camera feed, a closer look revealed gas pumps displaying the brand colors of a Finnish gas station chain. The footage also showed a small grocery store area and a quite large restaurant seating area.
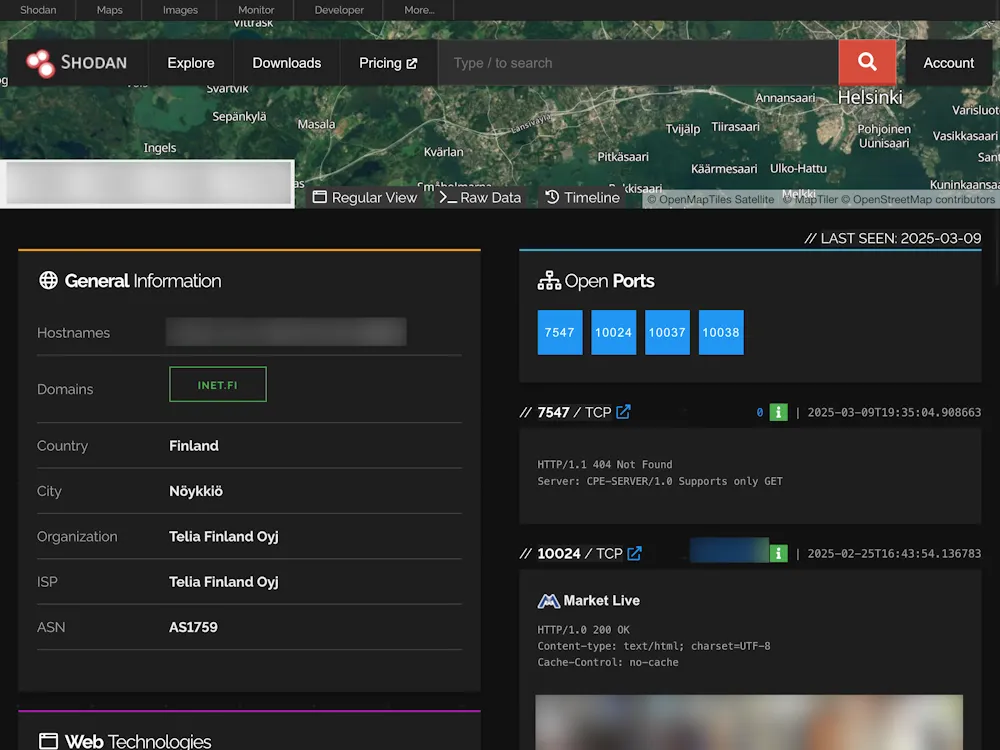
When checking the host’s history in Shodan, I was able to see another camera feed on a different port. It showed the cash register area, with a sign mentioning a car wash. At this point I had a rough idea of what the station looked like and what services it offered.
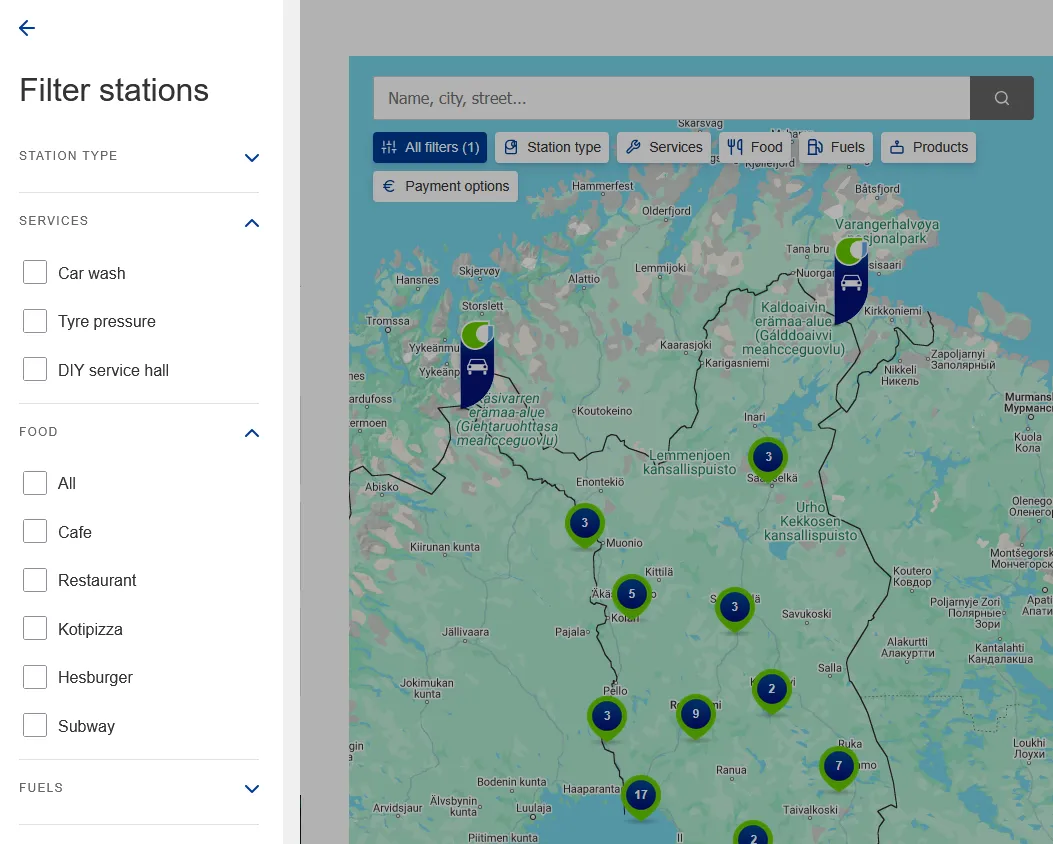
I went to the gas station chain’s website and used their station search to check, how many stations matched the criteria. By entering the services I saw in the footage, I was able to narrow down the search from around 200 stations to around 100 stations.
Mission impossible?
I was close to giving up. Manually going through over 100 stations would have taken forever. Then it hit me: I could automate it. I opened browser developer tools and found that the station search used a simple REST API to fetch the list.
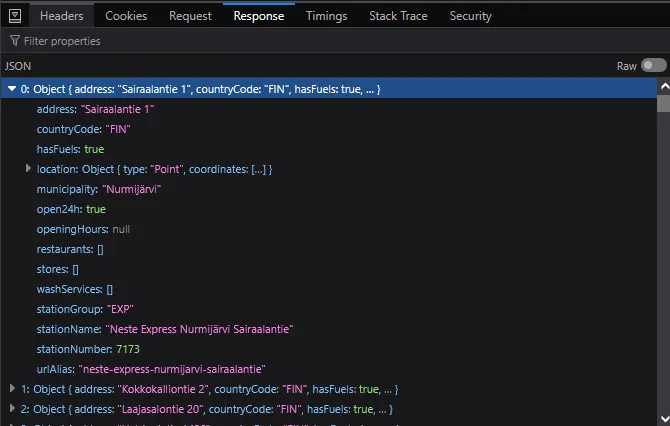
I pulled all the stations and wrote a quick Node.js script. It filtered the results and used Playwright to open Google Street View, capturing images of each station that matched the criteria. In the end, I had a folder with about 100 station photos. Around 90% were clear shots, but some missed the station entirely or were from bad angles.
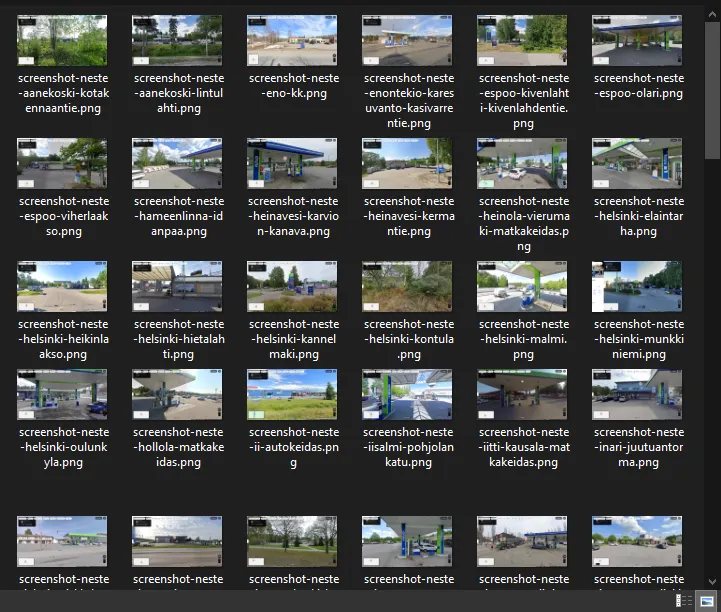
Then the manual work began: comparing these photos to the footage. I had a decent sense of what the station exterior should look like — entrance doors, windows, estimated size, and layout. The shadows outside the windows also gave away that the gas pumps and their shelter were right in front of the entrance. I had played quite a lot of Geoguessr, so I was (a bit over) confident in my skills.
The final stretch
It took around 10 minutes to go through all of the pictures and eliminate the ones that didn’t match. After all the filtering, I was left with around 10 stations. Next step was to compare the internal layout of the station. The best tool for this was again Google Maps as a lot of people upload pictures of the insides of the stations there.
There were some good clues in the feed, such as the floor tiles, their pattern, and the layout of the station interior. After a bit of searching, I was able to determine the location with a high degree of certainty. To confirm, I searched up the station on Google and found their Facebook page. On Facebook, they had posted a lot of pictures which confirmed the cashier area and the grocery store area. Mission accomplished!
Conclusion
The entire process took roughly three hours from start to finish. While the effort may not have been worth the time in a conventional sense, it was undeniably fun experience to use a bit of OSINT, overengineering, and a bit of Geoguessr-inspired intuition for a real life CTF challenge.
Once I had the location, I promptly reached out to the gas station and NCSC-FI to report the vulnerable device. Even though I never received a response from the gas station, the feed was quickly secured after the report.
This investigation highlighted a broader issue that many organizations face1: open camera feeds are more than just an oversight as they pose a serious security risk. Publicly accessible cameras can easily lead to physical security breaches and privacy violations, especially when they inadvertently capture customers or employees. In many cases, such exposures constitute a clear GDPR violation, as camera feeds are classified as personal data2 that must be protected.
Moreover, this risk isn’t confined to organizations alone. Many individuals have personal cameras at home that are left insecure, exposing intimate details of daily life to potential intruders. Whether in a commercial or private setting, these issues show that strong security, regular checkups, and following data protection laws are essential.